 VTP (VLAN Trunking protocol) is a protocol used to replicate the VLAN information across switches, however there are a few things that must be made clear…
VTP (VLAN Trunking protocol) is a protocol used to replicate the VLAN information across switches, however there are a few things that must be made clear…
- VLAN information will only be sent on trunk ports
- Only the VLAN identity is replicated, NOT which ports are configured to use that VLAN!
- Maintains database consistency through a common administrative domain. Switches that are not in the same VTP domain WILL NOT replicate!
- VTP advertisement are sent as multicast frames
- VTP advertisements are sent every 5 minutes or when there is a change.
So based on the above, when I create a new VLAN on a switch, that VLAN will be replicated to all other switches that are in the same VTP domain as the switch I made the change. This allows me to create a VLAN once and have the rest of the network learn about the creation via replication. Once the VLAN information has been replicated, then the switches will be able to allocate ports to the VLAN. At no time will a switch inform other switches about which ports are in which VLANS. VTP purely replicates the existence of the VLAN.
Further to the above, a switch can be configured to be in one of 3 modes of VTP (Server, Client, Transparent)
Server Mode
- Creates VLAN’s
- Modifies VLAN’s
- Deletes VLAN’s
- Sends and forwards the advertisements about the VLAN’s
- Synchronizes changes with other switches
- Saves the information to NVRAM (non volatile RAM)
Client Mode
- Cannot create, change or delete VLAN’s
- Forwards advertisements that it has received
- Synchronizes changes with other switches
- Does NOT save information to NVRAM, so when it’s rebooted it has to relearn the information
Transparent Mode
- Creates LOCAL VLAN’s only (This information will not be sent or advertised to any other devices)
- Modifies LOCAL VLAN’s only
- Deletes LOCAL VLAN’s only
- Sends and forwards advertisements that it has received from other devices
- Does NOT synchronize
- Saves its OWN configuration to NVRAM
Further to the above it’s important to understand that Transparent mode VTP is usually used in DMZ’s where the information should not be replicated or shared to any other devices on the network. Anything configured on a switch in Transparent mode, remains local to the device. It will not replicate the information with any other devices, and it will not learn any information from other devices.
In most cases, you would have a Server were changes to the VLAN’s would be done, and those changes would be replicated to all other switches in your network which would be running in client mode.
IMPORTANT NOTE: NEVER plug a new switch into a network unless you have configured it as CLIENT MODE!!!. If the new device was configured as a server and it happened to have a higher revision number (Synchronisation number) than the REAL server, the entire database will be overwritten and all VLAN configuration will be lost! This could cause the ENTIRE network to crash. This happens frequently when you have a test network, and you decide to use one of the test switches in the live network.
VTP pruning increases the available bandwidth by reducing unnecessary flooding traffic. This takes form in the following way…
If I have 6 switches in my network, and only 4 of them have any ports configured for VLAN 10, then only 4 switches would need to receive traffic destined for VLAN 10. The other 2 switches would learn about VLAN 10 through VTP and identify that they do not have any ports configured for that VLAN. They will then send a message (prune message) to all other switches asking them not to forward traffic destined for VLAN 10 to them as it will not be useful. If at any point these 2 switches DID have a port configured for VLAN 10, they would un prune themselves. Based on this, traffic destined for VLAN 10 would only be sent to switches that had ports configured to belong to VLAN 10. Please note, VTP does NOT send the port information to other switches, if a switch receives a prune message it would know not to forward traffic to that device for that particular VLAN, it does NOT know what the port configuration is of the neighbour switch.
In order to increase the security of the VTP information, as password can be set. Only devices that share the same password will be able to exchange information with each other. The password checking between devices is done through the use of MD5 hashing, so the password is never sent over the wire.
Additionally, there are currently 2 versions of VTP, VTP version 2 supports the same functions and features as version 1, but also includes the following
- Token Ring Support
- Unrecognized Type-Length-Values (TLV)
- Version-Dependent Transparent mode
- Consistency Checks
Below is the configuration breakdown used in the live demo.
AOIP.ORG_Switch# conf t
Enter global configuration mode
AOIP.ORG_Switch(config)# vtp mode server
Set the mode to Server
AOIP.ORG_Switch(config)# vtp domain AOIP
Defines the Domain name (it is CaSeSeNsItIvE)
AOIP.ORG_Switch(config)# vtp password aoip
Sets the password
AOIP.ORG_Switch(config)# vtp pruning
Turns on VTP pruning
AOIP.ORG_Switch(config)# vtp version 2
Changes to version to version 2 support
AOIP.ORG_Switch(config)#exit
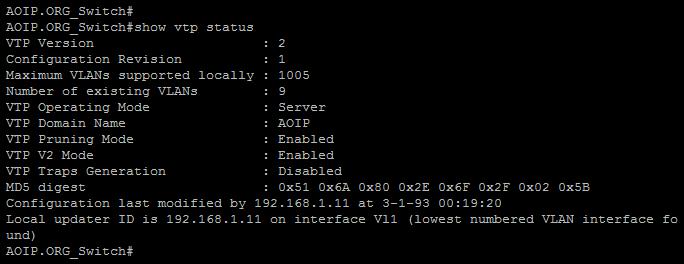
AOIP.ORG_Switch# show vtp status
Shows the current configuration of VTP as well as the replication revision number as seen in the below diagram.
Below is the Live Demo.





